Week 8: Win Registry
Part 3: Live Registry Acquisition
Forensically acquiring Windows Registry hives (SAM, Software, System, and Default) is crucial for digital investigations. While the Registry Editor allows viewing registry data, it does not provide a forensically sound method of acquisition. Instead, we must extract a verified copy of these hives for analysis.
However, directly copying the registry hives from WINDIR\System32\Config is restricted due to system permissions. The following methods outline how to properly acquire them.
1. Using FTK Imager
Steps to Acquire Registry Hives:
-
Open FTK Imager
- Launch FTK Imager on your system.
-
Initiate the Acquisition
-
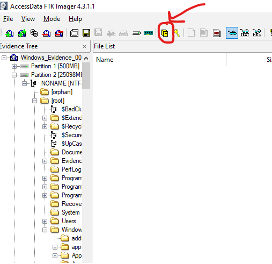
Click on the designated icon as shown below:
-
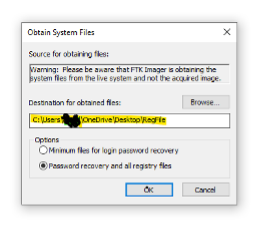
Select the second option and choose a location to save the file.
-
Once saved, you can explore the extracted hives separately for forensic analysis.
2. Using Zimmerman's Registry Explorer
Eric Zimmerman has developed several powerful tools for Digital Forensics and Incident Response (DFIR). One of the most useful tools for registry analysis is Registry Explorer, which provides enhanced capabilities for examining registry hives.
Key Features of Registry Explorer:
- Multi-Hive Loading: Load multiple registry hives simultaneously.
- Transaction Log Parsing: Merges data from transaction logs, resulting in a cleaner and more complete hive.
- Bookmarks for Key Artifacts: The built-in Bookmarks feature highlights forensically significant registry keys, allowing investigators to quickly locate important information.
We will explore these features in more detail in the upcoming tasks.
Part 1: Analysing Pre-Acquired Registry Hives
-
Download Registry Explorer from here, extract the folder, and run
RegistryExplorer.exeasAdministrator. -
If the software does not open, install the required .NET Runtime from here, then try running Registry Explorer again.
-
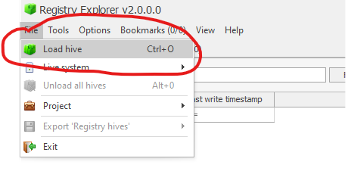
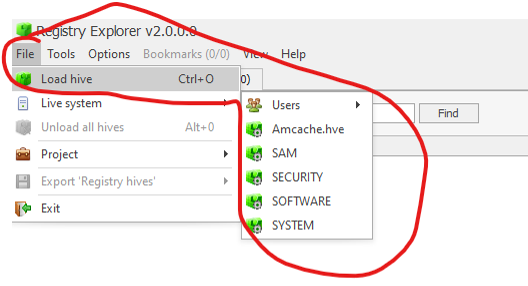
Load the acquired registry hives from FTK Imager (Step 1). For this task, try loading the SAM and SECURITY hives.
Once loaded, you can explore registry keys, values, and forensic artifacts stored in the registry.
Part 2: Analysing Live (Current) Registry Hives
Registry Explorer also allows you to analyse live (current) registry hives directly from the system.
To load live registry hives, follow these steps:
- Open Registry Explorer.
- Select File > Load Live Registry.
- Choose the desired hive (e.g.,
SAM,SYSTEM, orSOFTWARE). - Begin forensic analysis.
Live registry analysis allows investigators to examine system configurations and user activity in real time.
NEXT: you can navigate through the registry and try to look up for the information needed.
Data You Might Want to Look Up
During forensic analysis, specific registry keys provide critical information about the system. Below are some essential registry keys and related questions to investigate.
1. OS Version
To determine the Windows OS version, refer to the following registry key:
| Information | Registry Path |
|---|---|
| OS Version | SOFTWARE\Microsoft\Windows NT\CurrentVersion |
Question:
What is the Current Build Number of the machine under investigation?
Answer: __________
2. Computer Name
Identifying the computer name is crucial in forensic analysis to confirm we are examining the correct system.
| Information | Registry Path |
|---|---|
| Computer Name | SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName |
SYSTEM\ControlSet001\Control\ComputerName\ComputerName |
Question:
What is the Computer Name of the system?
Answer: __________
3. Time Zone Information
Establishing the time zone of the machine ensures accurate chronological event analysis.
| Information | Registry Path |
|---|---|
| Time Zone Info | SYSTEM\CurrentControlSet\Control\TimeZoneInformation |
SYSTEM\ControlSet001\Control\TimeZoneInformation |
Question:
What is the value of TimeZoneKeyName?
Answer: __________
4. Network Interfaces and Past Networks
The network interfaces present on the machine can be found in the following registry keys:
| Information | Registry Path |
|---|---|
| Network Interfaces | SYSTEM\CurrentControlSet\Services\Tcpip\Parameters\Interfaces |
SYSTEM\ControlSet001\Services\Tcpip\Parameters\Interfaces |
Each network interface is represented by a GUID subkey, containing TCP/IP configuration details, including:
- IP addresses
- DHCP IP address
- Subnet Mask
- DNS Servers
Question:
What is the DHCP IP address of the machine?
Answer: __________
5. Past Networks
To identify past networks the system connected to, check these registry keys:
| Information | Registry Path |
|---|---|
| Past Networks | SOFTWARE\Microsoft\Windows NT\CurrentVersion\NetworkList\Signatures\Unmanaged |
SOFTWARE\Microsoft\Windows NT\CurrentVersion\NetworkList\Signatures\Managed |
These keys provide information about previous network connections, including the last connection time, which can be determined by checking the registry key's last write time.
6. Autostart Programs (Autoruns)
The following registry keys contain information about programs or commands that automatically run when a user logs in:
| Information | Registry Path |
|---|---|
| Autostart Programs | NTUSER.DAT\Software\Microsoft\Windows\CurrentVersion\Run |
NTUSER.DAT\Software\Microsoft\Windows\CurrentVersion\RunOnce | |
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce | |
SOFTWARE\Microsoft\Windows\CurrentVersion\policies\Explorer\Run | |
| Recommended Key | SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
Question:
How many programs are set to autorun on this system?
Answer: __________
7. SAM Hive and User Information
The Security Account Manager (SAM) hive contains crucial data about user accounts, login activity, and group memberships.
| Information | Registry Path |
|---|---|
| User Information | SAM\Domains\Account\Users |
Question:
What is the RID (Relative Identifier) of the Guest Admin account?
Answer: __________
These registry keys provide valuable forensic insights into system configuration, user activity, and security settings. Analysing them correctly can help reconstruct events and verify critical system details.
Best, Ali
