Week 4 - Anti Forensics Techniques: Lab 2 - Password Cracking Lab
Learning Objectives
- Demonstrate and articulate the concept of a brute force password attack and a dictionary attack.
- Use John the Ripper to crack hashed passwords.
- Demonstrate the use of password salting and peppering.
Prerequisites: Check John the Ripper and (optional) with Webpack
You will use KALI VM for this lab too.
Before you start, check whether John the Ripper is installed on your Kali VM:
which john || john --version || echo "john not found"
If John is not installed, install it:
sudo apt update
sudo apt install -y john john-data
Notes about provided files
The files passwords.txt (download from here) and pass.txt (downlaod from here), are also on Moodle copy them to the VM.
Activity 1: Background
Familiarise yourself with hash functions and password storage:
- OWASP Password Storage Cheat Sheet: https://cheatsheetseries.owasp.org/cheatsheets/Password_Storage_Cheat_Sheet.html
- Online hash tool: https://www.fileformat.info/tool/hash.htm
Activity 2: A Brute Force Password Attack
- If you have not done so yet, please update your Kali system:
sudo apt-get update
-
Download
passwords.txtto your Downloads folder on the Kali VM. -
Open a terminal and copy the file to
/usr/sbin:
cd ~/Downloads
sudo cp passwords.txt /usr/sbin
- Change to
/usr/sbin:
cd /usr/sbin
- Run John the Ripper using the raw-MD5 format:
sudo john --format=raw-MD5 passwords.txt
- Display cracked passwords:
sudo john --show --format=raw-MD5 passwords.txt
Activity 3: Crack the Passwords (SHA-256)
- Download
pass.txtto your Downloads folder and save it to/usr/sbin:
sudo cp ~/Downloads/pass.txt /usr/sbin
cd /usr/sbin
pass.txtcontains usernames and SHA-256 hashed passwords. Try to crack them using John. Hint: similar approach to Activity 2 but adjust the format option.
Example commands to try:
sudo john --format=raw-sha256 pass.txt
sudo john --format=raw-sha256 --wordlist=/usr/share/wordlists/rockyou.txt pass.txt
- Use
--showto list found passwords:
sudo john --show --format=raw-sha256 pass.txt
Activity 4: Create and Exchange
- Create a password file with username and SHA-256 hashed passwords. Example format:
- You can use nano tool to create and save the file or any other editor
password_user1:5e884898da28047151d0e56f8dc6292773603d0d6aabbdd62a11ef721d1542d8
password_user2:2c1743a391305fbf367df8e4f069f9f9eda3c0d5b2a6b3d4f1c2e3a4b5c6d7e8
-
Use the online hash tool to compute SHA-256 values for each password : https://www.fileformat.info/tool/hash.htm
-
Save your file and, if possible, swap with a classmate.
-
Run John the Ripper against the received file:
sudo john --format=raw-sha256 received_file.txt
sudo john --show --format=raw-sha256 received_file.txt
- If passwords are not found, change the passwords and try again.
Activity 5: A Dictionary Attack
In this task you will deploy John the ripper, so it uses a wordlist to compares the hashes of the words present in the dictionary with the password hash.
- Locate available wordlists:
locate wordlist
- Copy the rockyou wordlist to
/usr/sbin:
sudo cp /usr/share/wordlists/rockyou.txt.gz /usr/sbin
cd /usr/sbin
sudo gzip -d rockyou.txt.gz
- Run John with the wordlist for raw-MD5:
sudo john --wordlist=rockyou.txt --format=raw-MD5 passwords.txt
- Show cracked entries:
sudo john --show --format=raw-MD5 passwords.txt
Activity 6: Check for Prior Data Breach
Check to see if one of your online accounts has already been breached. Type in one of your email accounts or usernames to see if it has already been compromised in a data breach.
- Visit Have I Been Pwned: https://haveibeenpwned.com/
- Check the Passwords page: https://haveibeenpwned.com/Passwords
- Test some email addresses or passwords to see if they appear in known breaches.
Activity 7: Password Salting
In this task we will explore the concept of password salting. You will learn 4 different ways in which you can hash passwords whilst adding ‘salt’.
Salting is the practice of adding a unique random string to a password before hashing.
password + additional string (salt) → hashing algorithm → hashedPasswordAndSalt
- The “additional string”, or the salt, is normally randomly generated however, it you wanted you could specify what you want the salt to be. We will look at this in a later task.
- To further learn about the concept and implementation of password salting, please use the following links as a starting point:
7.1 How Kali stores passwords
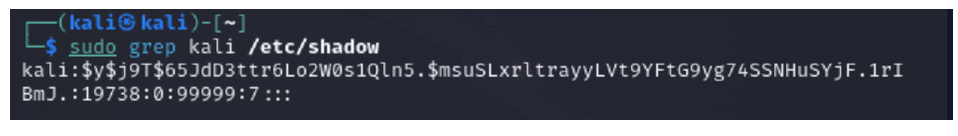
To determine the hash algorithm used to hash the passwords for a username, in this case “kali”, enter the command in the Kali terminal:
sudo grep kali /etc/shadow
- This command shows a list of the password hashes of all users in one go.
- The output you see should be similar to the one shown in the screenshot below, where the structure of the output line is as “username”
:$hashingAlgorithm$salt$hash. - Of course, the hash itself will be unique as when a password is set, a random string is added to the password and then hashed using a chosen algorithm
- To create a new user and set a password, enter the following commands:
sudo adduser <username>
- where
is replaced with your chosen word. - You will be prompted to enter a password and to confirm the password. It will also ask to confirm details (this part you can skip by pressing the ENTER key.)
- To check how the newly set password for the newly added user is stored in the
/etc/shadowfile, enter in the following command:
sudo grep <username> /etc/shadow
7.2 Password Hashing using OpenSSL
For this activity, you will use the openssl passwd command to generate a hash for the password “apple”. Implementing 4 different method, out of which 3 will generate their own salt and the last you will be able to choose your own “salt”
1 Enter the following in the terminal:
openssl passwd -6
-
You will be prompted to enter and verify a password, enter the password as
apple. -
At the end of the process, a line will be generated.
Q: Which hash algorithm was used the hash the password and salt? How do you know? What prompted it to hash using that algorithm?
2. Enter the following in the terminal:
openssl passwd -5 apple
Q: Which hash algorithm was used the hash the password and salt? What is the difference between the command used in step 27 and step 26?
3.
If not done so already, please navigate to the /usr/sbin directory. Create a text file containing the password apple, save it as classified.txt in the /usr/sbin directory.
In the terminal, enter the following command:
openssl passwd -1 -in classified.txt
Please capture an evidential screenshot of your results and insert here:
4
Using John the Ripper, are you able to crack the password?
Hint: use --format=md5crypt-long an option in the command
Please capture an evidential screenshot of your result and try to anylyse it
5
In the terminal, enter the following command:
openssl passwd -6 –salt <SALT>
- Where
<SALT>is replaced with a random string (35 characters) of your choice. - You will be prompted to enter a password, enter the password as
apple. - At the end of the process, a line will be generated.
- Please capture an evidential screenshot of your results and try to anylyse it
Activity 7.3: Can they crack the salted password?
- In a terminal, enter the following command:
sudo openssl passwd -1 –salt <SALT>
-
Where
is replaced with a random string (35 characters) of your choice. -
You will be prompted to enter a password - enter a password of your own choice. It is suggested to use a common dictionary word for this activity, in real life of course you will make it complicated.
-
Navigate to the /usr/sbin directory.
-
Create a text file containing the hash output generated in the following format:
username:<hash output>
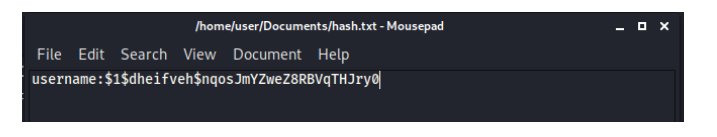
- Save it as “hash.txt” in the /usr/sbin directory.
- If possible, exchange the file with a peer via email.
- Once you have received the file from your partner, save this file in /usr/sbin.
- Using John the Ripper, are you able to crack the password?
Activity 8: Investigate Peppering
Peppering is a strategy used for enhancing the security of password storage by adding an additional layer of protection beyond hashing and salting. (OWASP Password Storage Cheat Sheet)
- For this task investigate the peppering process and provide summary with an example for the process.
Activity 10: Sources for Dictionary Creation
List potential sources for building a dictionary for a dictionary attack.
---
